Itential Configuration Manager
Validate Changes & Ensure Configuration Consistency with AI-Powered Compliance
Capabilities
Define the Standard, Detect the Drift, Prove Compliance
Whether you’re enforcing golden configs or responding to security threats, Itential’s Configuration Manager lets you standardize once, validate continuously, and remediate automatically – with audit-ready evidence for every action.
Always Compliant
Continuous validation across network, security, and cloud.

Drift-Free Infrastructure
Detect and remediate config drift automatically.

Evidence On-Demand
Immutable audit trail for every config change.

AI-Ready
Compliance checks and remediation exposed safely to agents via MCP.
Golden Configuration Templates
Standardize Configs Once, Enforce Everywhere
- Create flexible, reusable Golden Configuration templates with variables, inheritance, and iteration to eliminate template sprawl
- Lock down critical configs like ACLs and route policies with intelligent rules for ordered lists
- Manage templates in a tree hierarchy where changes automatically cascade to child configs
- Support any device or service across physical and cloud infrastructure
Continuous Compliance Validation
Catch Drift Before It Becomes an Outage
- Schedule proactive compliance checks to detect non-compliant assets before they cause issues
- Validate changes before activation to prevent misconfigurations from reaching production
- Compare intended vs. actual state and flag drift for immediate remediation
- Build guardrails for self-serve infrastructure with built-in validation on every change
AI-Ready Compliance
Let Agents Detect Drift & Propose Fixes, Within Guardrails
- Expose compliance checks and remediation workflows as APIs for pipelines and Itential MCP-connected agents
- AI agents query compliance posture, identify drift patterns, and generate remediation proposals – all validated through governed workflows
- Enforce policy checks, risk-tiered approvals, and pre/post validation on every agent-initiated action
- Capture complete audit trails (who/what/when) so AI-driven compliance remains traceable and accountable

Automated Remediation
From Detection to Resolution in Minutes
- Automate remediation workflows that resolve non-compliant issues without manual intervention
- Respond to active security threats in real-time by immediately detecting and fixing non-compliant devices
- Identify and eliminate persistent misconfigurations causing recurring network issues
- Execute compliance checks and remediations through orchestrated, multi-step workflows
Unified Device Management
One Inventory for All Your Infrastructure
- Consolidate network and cloud devices into a single, federated inventory for unified compliance auditing
- Automate configuration backups and retrievals across physical and cloud infrastructure
- Create flexible device groups by OS type, function, location, or any criteria
- Manage critical configs across any domain, network, or cloud vendor
Compliance Plans & Reporting
Prove Compliance Without the Spreadsheet Scramble
- Generate on-demand compliance reports instantly for any device or group
- Develop comprehensive compliance plans covering data center, cloud, and security resources
- Schedule automated reporting for continuous application oversight
- Export immutable logs and evidence packages that shrink audit prep from weeks to days
IT System Integration
Connect Compliance to Your Change Process
- Automatically update ITSM systems like ServiceNow with compliance events and remediation results
- Orchestrate compliance workflows that integrate with network discovery and monitoring systems
- Build incident response workflows triggered by telemetry and observability events
- Maintain full traceability from compliance detection through remediation completion
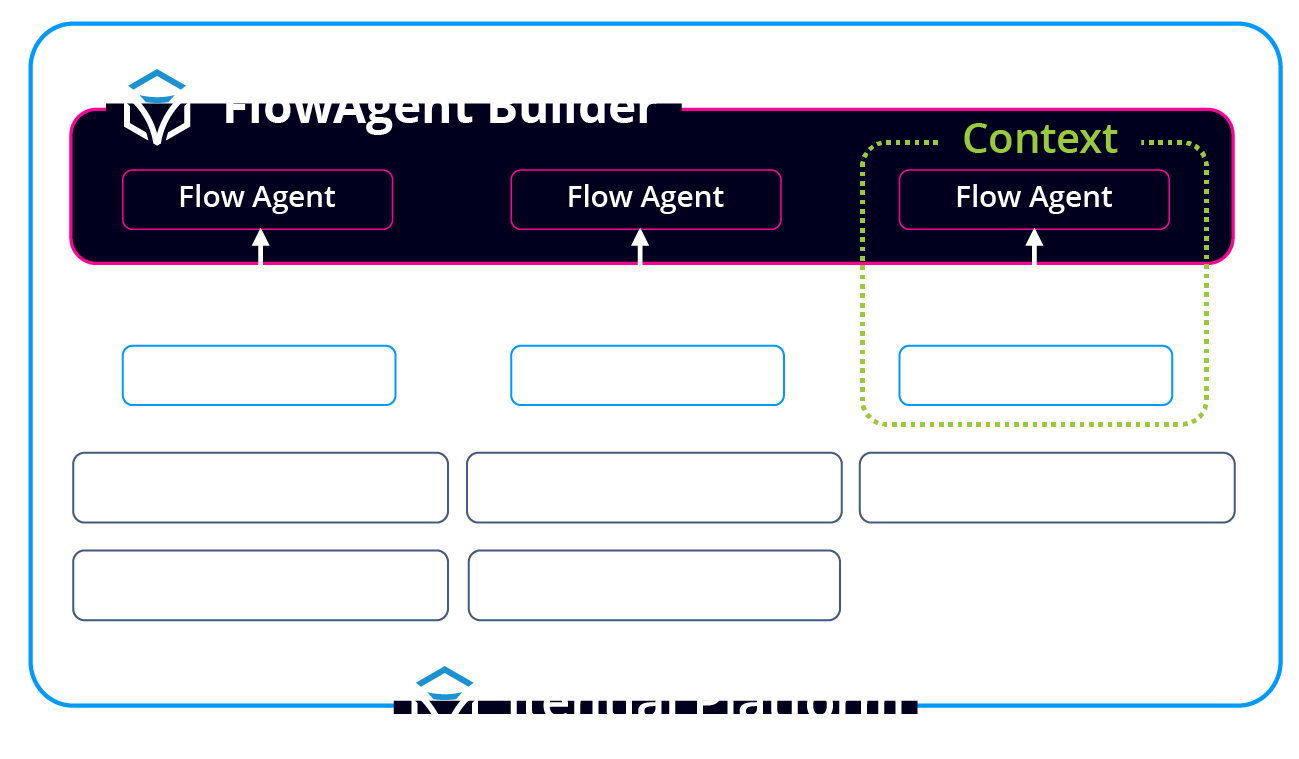
FlowAI
AI Agents + Configuration Manager: Continuous Compliance Through Agentic Operations
Configuration Manager serves as the compliance enforcement layer that AI agents can query and act through safely. Through Itential’s Model Context Protocol (MCP) and FlowAI, agents can detect drift, analyze compliance posture, and propose remediation – all executed through governed workflows with enterprise guardrails.
- AI Agents Query Compliance Posture
Agents continuously monitor config state, identify drift patterns, and analyze compliance across your entire infrastructure – providing real-time visibility into security and policy violations. - MCP-Connected Compliance Actions
AI agents propose config changes and remediation through MCP, and every request flows through Configuration Manager’s validation, approval gates, and policy enforcement – AI never bypasses compliance. - Intelligent Drift Detection
Agents can identify configuration drift that would introduce security risks or performance issues, then propose and execute remediation through approved workflows with complete audit trails. - Compliance-as-Code for AI
Configuration policies and golden templates become the guardrails that AI agents operate within – ensuring every agent-driven change maintains compliance with your standards.
AI-Powered Compliance Engine
One Platform. Many Teams. Centralized Compliance.
Itential enables security, operations, engineering, and platform teams to manage configuration compliance from a centralized, governed platform – aligned to your policies and ready for AI.
Security & Compliance
Enforce golden configs, detect drift, and auto-remediate non-compliance with continuous validation and immutable audit logs for regulatory requirements.

Engineering & Operations
Validate changes before deployment with built-in compliance checks. Eliminate manual config reviews and reduce change-related incidents.
Platform & AI Teams
Expose compliance checks and remediation as APIs to pipelines and agents – so AI can detect issues and propose fixes through governed, traceable workflows.
IT Leaders & Architects
Standardize how configs are managed and validated across domains. Get program-level visibility into compliance posture and consistent evidence at enterprise scale.
Frequently Asked Questions
How does Itential enforce configuration compliance?
Define golden configs once; Itential continuously checks devices, detects drift, and remediates automatically.
How does this help Infrastructure teams with audits?
Continuous validation and immutable logs shrink audit prep from weeks to days. Audit evidence is always current and exportable.
Can Itential block non-compliant changes?
Yes. Guardrails can block, require approvals, or auto-rollback non-compliant changes.
Will this work with Ansible and Terraform?
Yes. Playbooks and plans are reused inside Itential, with compliance and audit layers added.
Does it support multi-domain compliance?
Yes. Config policies can span data center, WAN, campus, cloud, and firewalls from a single application.
How do AI copilots use Configuration Manager?
FlowAgents, apart of FlowAI, can query drift and compliance posture, generate config policies, propose remediation workflows, and analyze security vulnerabilities – while Configuration Manager enforces validation, approvals, and audit trails for all agent-initiated changes.
- AI-Driven Golden Configuration Trees: End Compliance Fire Drills, Forever
- Security Vulnerabilities Top of Mind? How to Prevent Network Breaches with Automated Audit & Remediation
- How NetDevOps Teams Can Build Testing & Validation into their Network Automations
- From Chaos to Compliance: How a Utilities Company Adopted Itential to Modernize Configuration Management
- How Itential’s Compliance Plans Transform CLI & API Compliance within One Platform
- Itential Recognized as a Fast Mover in the 2025 GigaOm Radar for Network Validation, for the Fourth Consecutive Year
- How SOC Teams Can Self-Serve Hybrid Network Security Services with Itential
- How to Automate Scanning & Remediation for Network Device Security Vulnerabilities with Itential
- How a Global Biotech Company Standardized Network Automation to Eliminate Errors & Enable Safe, Secure Self-Service
- How to Leverage Itential MCP & Agentic AI to Reduce Network & Security Troubleshooting Time
- Itential’s Golden Configuration Methodology for Achieving Network Consistency
- Itential Configuration Manager Overview
- Compliance Plans & Compliance for Ordered Lists
- How to Execute Compliance & Remediation of Vulnerable Features on Cisco IOS XE Devices
- Automating Configuration, Compliance, & Remediation Across Network & Cloud Infrastructure with Itential
- How to Audit Network Security Vulnerabilities from Cisco PSIRTs with Itential’s Automated Configuration Compliance
- How to Build a Golden Configuration for Network Devices with Itential
- Building Compliance Rules for Ordered Lists in CLI Configurations with Itential